AUTOMATE FILE ENCRYPTION AND DECRYPTION
VisualCron is an automation, integration and task scheduling tool for Windows
Summary
Encryption and decryption exists in many forms within our organizations. There are file transfer protocols that are using encryption to secure file transfer, similar to waht we have for email as well. Besides encrypting the actual transfer of a message or file, the file itself can be encrypted.
Symmetric and asymetric encryption
Symmetric encryption is the oldest and best-known technique. A secret key, which can be a number, a word, or just a string of random letters, is applied to the text of a message to change the content in a particular way. This might be as simple as shifting each letter by a number of places in the alphabet. As long as both sender and recipient know the secret key, they can encrypt and decrypt all messages that use this key.
The problem with secret keys is exchanging them over the Internet or a large network while preventing them from falling into the wrong hands. Anyone who knows the secret key can decrypt the message. One answer is asymmetric encryption, in which there are two related keys - a key pair. A public key is made freely available to anyone who might want to send you a message. A second, private key is kept secret, only you know it.
Any message (text, binary files, or documents) that are encrypted by using the public key can only be decrypted by applying the same algorithm, but by using the matching private key. Any message that is encrypted by using the private key, can only be decrypted by using the matching public key.
This means that you do not have to worry about passing public keys over the Internet (the keys are supposed to be public). A problem with asymmetric encryption, however, is that it is slower than symmetric encryption. It requires far more processing power to both encrypt and decrypt the content of the message.
PGP and VisualCron
VisualCron supports the OpenPGP standard for asymmetric and symmetric encryption. VisualCron uses a central PGP key ring manager for creating and storing the PGP key rings that later can be used in Tasks. The created keys supports the RSA and Elgamal /DSS encryption standards with key sizes from 512 to 4096.
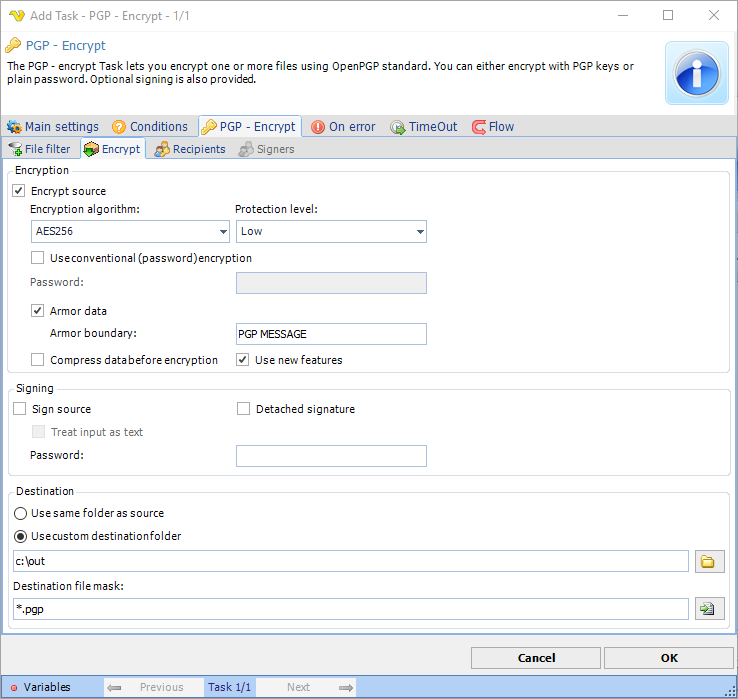
Screenshot of the PGP Task in VisualCron
With the PGP Encrypt and PGP Decrypt Tasks you can encrypt, compress and sign any file using the following encryption algorithms:
- AES128
- AES256
- CAST5
- 3DES / TripleDES
- IDEA
- BLOWFISH
- TWOFISH
Symmetric encryption and VisualCron
VisualCron offers direct symmetric encryption and decryption with the following encryption algorithms:
- 3DES / TripleDES
- DES
- RC2
- Rijndael
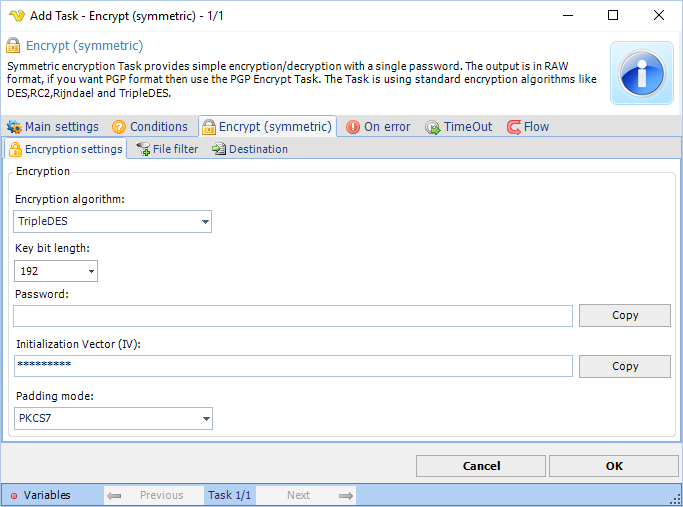
Screenshot of the Encrypt (symmetric) Task in VisualCron